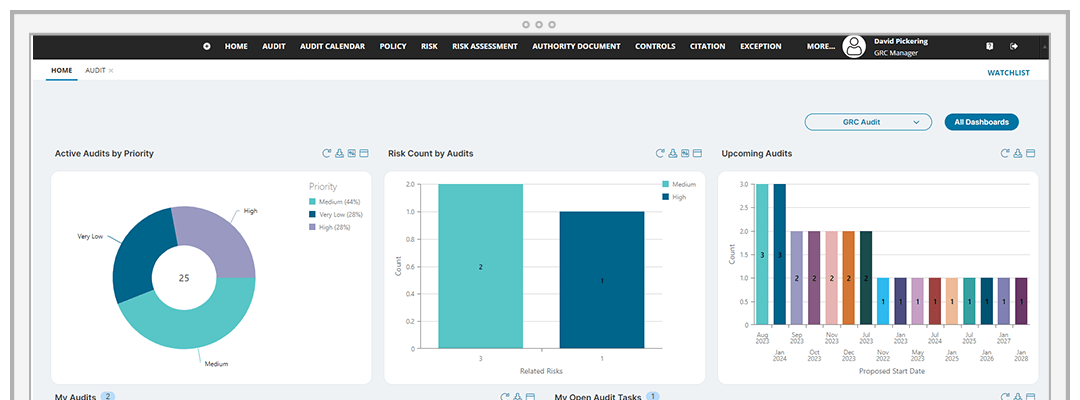
Companies invest heavily in cyber-threat detection and prevention technologies, but still manage regulatory and contractual compliance manually. Ivanti Neurons for GRC provides a simple way to unify your GRC management so all authority documents, citations, controls, and risks are tracked in a single system. It's compliance, automated.
Automate compliance processes
Ease the compliance burden with quick and easy regulatory documentation imports to map citations with security and compliance controls.